Free Download Software Hacker Facebook Terbaru
Free Download Software Hacker Facebook Terbaru Rating: 3,7/5 8674votes
HACKING FACEBOOK STEP BY STEP Facebook is one of the most important social networks around the world these days. It has millions of users and more and more are joining every day.
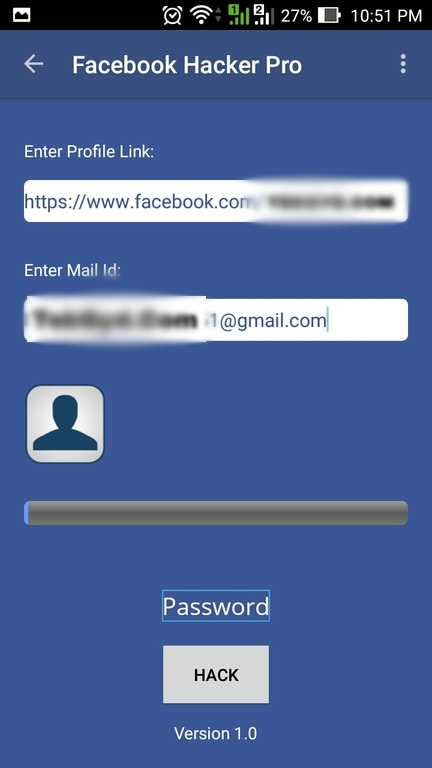
Numbers like this are not sufficiently striking until we notice that our neighbors have one, and not just them but also our family, our coworkers and our best friends have one too. Knowing this makes us want to hack the Facebook account of someone in particular, any person we would like to know more about for no reason. We are an anonymous group of Internet users seeking to access Facebook security since 2016, and currently in 2017. One of the links that can be trusted is the one that we offer, which is one of the few reliable free online services that allows you to obtain users' Facebook accounts essentially for free. How to use this system by pasting a link from Facebook In order to make this website to perform its function perfectly, there are two ways that you can insert the link, and both of them work fine. Here is an example of how to enter the correct link in the system quickly and easily: This example is from the CEO of Facebook, Mark Zuckerberg. As you can see, you can insert either the user link or the profile photo, as shown in the image.
Download FREE AVG antivirus software. Get protection against viruses, malware and spyware. Easy-to-use virus scanner for PC, Mac & mobile. Download TODAY. Nah cekarang fary mau membahascara hack akun facebook orang dengan menggunakan software Black Code dari Maroko untuk caranya yuk kita bahas xiixxi!! Tapi yang jelas software ini wajib dan harus sambil online dan untuk mempermudah hack akun seseorang target harus online sebelumnya yuk kita download.
Once you have obtained either of those links, you can continue entering any of those on this page. Just copy and paste the link of the users that you've decided to hack. In this particular case, you will paste the link of the Facebook user whose email address and password you want to get, in order to access his or her private conversations, photos, and many other things. How to enter the link of the target's profile on the correct page Once you have entered the link on this website, as mentioned before, either with 1) the user profile link or 2) profile photo, you should see the hacking process of the person that you have decided to hack, as shown below: 3. How do I know if I entered the link correctly? Once you have entered the link of the person you decided to hack, you should be able to see their Facebook information, such as name, last name and the person's profile photo. If this information is not shown correctly after trying with the link of the profile or the link of the profile picture, then you can and we will help you with the process. You can try once again to do the appropriate steps so you can hack a Facebook 2017.
If you got an error after you entered the link, then double check that you have entered this link with 'no spaces'. How long does the hacking process take? The process of hacking any person's account takes approximately 1 to 5 minutes. This is because we send a code injection to the database of the social network, Facebook, which is how we get the password. This process will take a little bit longer if the person change their information on Facebook to private, such as date of birth, address, phone number, friends, groups, persons and pages that he or she is following, and also more.
Don't worry, the process is 100% functional even if it takes a little more time. You have to trust that you will get access to the Facebook account you want. Results of the hacked account After you wait for the results to appear, you should be able to see key parts of the information. It means that the Facebook that you entered has been hacked and our system has the information such as: email, cell phone number, and most importantly, the password. When the hacking system is finished, you have to wait few minutes. The website will indicate that the data for the hacked Facebook account are available, and then it will redirect to a page in which you won't have to pay any money to obtain the username and the password.
That means that you won't have to pay money to hack someone else's Facebook, because the system will always be free. How to get the email, phone number and password from the hacked account You have 2 methods where you can get the data from Facebook for free. The first involves referrals. These links should be shared with at least 5 contacts and they have to click on your link; this helps us verify that the system is not being used in a malicious way or by a robot trying to affect our site, sending a large volume of requests to our servers. Once you have shared your referral links, a file will be sent to your email with the data of the hacked account, or you might be able to see the hacked data in the same link. But referral links are not the only method to easily hack a Facebook account. There is also a second method, which is filling out an anonymous survey.
This anonymous survey is not an advertising method. This is a mechanism that generates a small income for this website, but if we look carefully, this is a mechanism used so that not just anyone can get access to the Facebook account data entered, but only you can have it. That's the main reason to do the survey: to guarantee that just you, and nobody else, have access to the information. After complying with any of the non-monetary compensation methods for the website, either by referral or survey, you have to enter your email here: and we will send a text file where you can find the user and password of the hacked account. You can also save the link because the data is registered in our database automatically.
Both methods will let you get the information of the victim you've hacked in 2017. Download Lagu Gratis Labrinth Beneath Your Beautiful. Tips to follow after getting your target's information When you finally get the account of the victim, you can do whatever you want, but.
There is a tip that you should follow. If you wanted the information to spy on them (which is the most common), you should look at everything you want but without changing anything, because you don't want to alert the real owner of the account that maybe you have access to their account. If you do it right, you could get the access to their personal information, conversations, notifications history and to their photo gallery and videos, in which there might be content that is not public for everyone and might be interesting. You can download a copy with all the information of your victim easily. With this information, you'll be able to see and read all the things that this person has done from the very beginning until today, such as posts, photos, shared videos, messages, conversations and a lot of other info. This is the best way to know what this person is doing without using expensive or useless hacking software. How does this website work for hacking Facebook 2017?
This question can be answered in depth, but we don't want you to deal with complex computing terms. However, it is possible to explain in a simple way: howto.piraterfaceook.com has a whole set of online tools used to breach the security of the social network Facebook. This is possible through mechanisms that only expert security programmers can understand, but you don't need to have many computer skills because this website was designed so that anyone can use it. The data shown are from real people who have used this system. For security reasons, we have decided to hide them for the privacy of our users. If you pay attention to the image, you can see that these are real hacked accounts in 2017.
Data generated by you will only be seen by you, so you won't have to worry about anything because we have a reliable page that does not provide any information to third parties. This system uses web scripts to breach Facebook's security. This is called code injection; we analyze the link required to perform the hacking process. Each Facebook link consists of a domain with a set of codes representing IDs for any user's data. For example, the URL of a contact consists of the Facebook domain, a bar and the ID of the account's owner.
This ID is not easy to obtain, but our system can determine where certain information comes from. Howto.piraterfaceook.com knows that no system is 100% secure from hacking, which means that anyone can get into Facebook's data, and that's what we do now.
New SQL Injection Lab! Skillset Labs walk you through infosec tutorials, step-by-step, with over 30 hands-on penetration testing labs available for FREE! Internet is now the basic need of our daily life. With the increasing use of smartphones, most of the things are now online.
Every time we have to do something, we just use our smartphone or desktop. This is the reason wi-fi hotspots can be found everywhere. People also use wireless in their home network to connect all devices. Every person can see the neighborhood wi-fi networks in the system, and they want to use it for free.
But most these networks are secured with a password key. You need to know this security key to access the network. When your own network is down, you will desperately want to connect to these neighborhood networks.
For this, people generally search for wi-fi password cracking tools to get unauthorized access to those wireless networks. Ethical Hacking Training – Resources (InfoSec) Sometimes when you are on a network, you also want to check what is happening on the network. This happens mostly in big organizations, when an employer wants to check who is doing what in the network. For these things, there are a few network hacking tools available that let users analyze packets and see what other users are doing. In this article, I am going to discuss wireless security and best wi-fi password cracking or recovery tools. I will explain the kind of encryption wireless networks use and how these tools can crack the networks to get access.
We will also see what tools let users monitor networks. Wireless Networks and Hacking Wireless networks are based on IEEE 802.11 standards defined by IEEE(Institute of Electrical and Electronics Engineers) for ad hoc networks or infrastructure networks.
Infrastructure networks have one or more access points which coordinate the traffic between the nodes. But in ad hoc networks, there is no access point; each node connects in a peer-to-peer way. Basically there are two types of vulnerabilities which can be found in the Wireless LAN. One is poor configuration and the other is poor encryption. Poor configuration is caused by the network admin who manages the network. It may include the weak password, no security settings, use of default configurations, and other user related things. Poor encryption is related to security keys used to protect the wireless network.
It is there because of issues in WEP or WPA. WEP and WPA WEP and WPA are the two main security protocols used in Wi-Fi LAN. WEP is known as Wired Equivalent Privacy (WEP). It is a deprecated security protocol which was introduced back in 1997 as a part of original 802.11 standards.
But it was weak, and several serious weakness were found in the protocol. Now, this can be cracked within minutes. So, a new kind of security protocol was introduced in 2003. This new protocol was Wi-Fi Protected Access (WPA). It has mainly two versions, 1 and 2 (WPA and WPA2).
Now it is the current security protocol used in wireless networks. To get unauthorized access to a network, one needs to crack these security protocols. There are many tools which can crack Wi-Fi encryption.
These tools can either take advantage of WEP weaknesses or use bruteforce attacks on WPA/WPA2. I am sure now you know that you should never use WEP security.
Basically wireless hacking tools are of two types. One of which can be used to sniff the network and monitor what is happening in the network. And other kinds of tools are used to hack WEP/WPA keys. These are the popular tools used for wireless password cracking and network troubleshooting. Aircrack Aircrack is one of the most popular wireless passwords cracking tools which you can use for 802.11a/b/g WEP and WPA cracking. Aircrack uses the best algorithms to recover wireless passwords by capturing packets. Once enough packets have been gathered, it tries to recover the password.
To make the attack faster, it implements a standard FMS attack with some optimizations. The company behind the tool also offers an online tutorial where you can learn how to install and use this tool to crack wireless passwords.
It comes as Linux distribution, Live CD and VMware image options. You can use any of these. It supports most of the wireless adapters and is almost guaranteed to work. If you are using a Linux distribution, the only drawback of the tool is that it requires deeper knowledge of Linux. If you are not comfortable with Linux, you will find it hard to use this tool. In this case, try Live CD or VMWare image. VMWare Image needs less knowledge, but it only works with a limited set of host OS, and only USB devices are supported.
Before you start using this too, confirm that the wireless card can inject packets. Then start WEP cracking. Read the online tutorial on the website to know more about the tool. If you will follow steps properly, you will end up getting success with this tool. AirSnort AirSnort is another popular tool for decrypting WEP encryption on a wi-fi 802.11b network. It is a free tool and comes with Linux and Windows platforms. This tool is no longer maintained, but it is still available to download from Sourceforge.
AirSnort works by passively monitoring transmissions and computing encryption keys once it has enough packets received. This tool is simple to use.
If you are interested, you can try this tool to crack WEP passwords. Cain & Able Cain & Able is a popular password cracking tool. This tool is developed to intercept network traffic and then discover passwords by bruteforcing the password using cryptanalysis attack methods.
It can also recover wireless network keys by analyzing routing protocols. It you are trying to learn wireless security and password cracking, you should once try this tool. Kismet Kismet is the wi-fi 802.11 a/b/g/n layer2 wireless network sniffer and IDS. It works with any wi-fi card which supports rfmon mode. It passively collects packets to identify networks and detect hidden networks. It is built on client/server modular architecture. It is available for Linux, OSX, Windows and BSD platforms.
NetStumbler NetStumbler is a popular Windows tool to find open wireless access points. This tool is free and is available for Windows. A trimmed down version of the tool is also available.
It is called MiniStumbler. Basically NetStumblet is used for wardriving, verifying network configurations, finding locations with a poor network, detecting unauthorized access points, and more. But the tool also has a big disadvantage. It can be easily detected by most of the wireless intrusion detection systems available. This is because it actively probes a network to collect useful information. Another disadvantage of the tool is that it does not work properly with the latest 64 bit Windows OS.
This is because the tool was last updated back in April 2004. It has been around 11 years since the last stable release of the tool. Download Netstumbler: 6. InSSIDer inSSIDer is a popular Wi-Fi scanner for Microsoft Windows and OS X operating systems. Initially the tool was opensource.
Later it became premium and now costs $19.99. It was also awarded as “Best Opensource Software in Networking”. The inSSIDer wi-fi scanner can do various tasks, including finding open wi-fi access points, tracking signal strength, and saving logs with GPS records. Download inSSIDer: 7. WireShark WireShark is the network protocol analyzer.
It lets you check what is happening in your network. You can live capture packets and analyze them. It captures packets and lets you check data at the micro-level.
It runs on Windows, Linux, OS X, Solaries, FreeBSD and others. WireShark requires good knowledge of network protocols to analyze the data obtained with the tool. If you do not have good knowledge of that, you may not find this tool interesting. So, try only if you are sure about your protocol knowledge. Download Wireshark: 8.
CoWPAtty CoWPAtty is an automated dictionary attack tool for WPA-PSK. It runs on Linux OS.
This program has a command line interface and runs on a word-list that contains the password to use in the attack. Using the tool is really simple, but it is slow. That’s because the hash uses SHA1 with a seed of SSID. It means the same password will have a different SSIM.
So, you cannot simply use the rainbow table against all access points. So, the tool uses the password dictionary and generates the hack for each word contained in the dictionary by using the SSID. The new version of the tool tried to improve the speed by using a pre-computed hash file. This pre-computed file contains around 172000 dictionary file for around 1000 most popular SSIs. Telecharger Windows 7 Titan 32 Bits Iso Burner more. But if your SSID is not in those 1000, you are unlucky. Download CoWPAtty: 9. Airjack Airjack is a Wi-Fi 802.11 packet injection tool.
This wireless cracking tool is very useful in injecting forged packets and making a network down by denial of service attack. This tool can also be used for a man in the middle attack in the network.
Download AirJack: 10. WepAttack WepAttack is an open source Linux tool for breaking 802.11 WEP keys. This tool performs an active dictionary attack by testing millions of words to find the working key. Only a working WLAN card is required to work with WepAttack. Download WebAttack: 11.
OmniPeek OmniPeek is another nice packet sniffer and network analyzer tool. This tool is commercial and supports only Windows operating systems. This tool is used to capture and analyze wireless traffic. But it requires you to have good knowledge of protocols to properly understand things. A good thing is that the tool works with most of the network interface cards available in market. This tool is used for network troubleshooting.
This tool also supports plugins, and 40 plugins are already available to extend the features of the tool. Download: 12. CommView for WiFi CommView for WiFi is another popular wireless monitor and packet analyzer tool.
It comes with an easy to understand GUI. It works fine with 802.11 a/b/g/n/ac networks.
It captures every packet and displays useful information as a list. You can get useful information like access points, stations, signal strength, network connections and protocol distribution. Captured packets can be decrypted by user-defined WEP or WPA keys. This tool is basically for wi-fi network admins, security professionals, and home users who want to monitor their wi-fi traffic and programmers working on software for wireless networks.
Download CommView: 13. CloudCracker CloudCracker is the online password cracking tool for cracking WPA protected wi-fi networks. This tool can also be used to crack different password hashes. Just upload the handshake file, enter the network name and start the tool. This tool has a huge dictionary of around 300 million words to perform attacks.
Try Cloudcracker: Conclusion In this post, I discussed 13 wireless hacking tools. A few wireless hacking tools are for cracking the password to get unauthorized access, and a few are for monitoring and troubleshooting the network. But most of the people really interested in tools to crack wireless hotspots just want to get free Internet access.
The above collection also contains those tools which try a dictionary attack to crack wi-fi passwords to allow you to get free Internet access. But be sure not to use these tools in a risky place. Hacking wireless networks to get unauthorized access may be a crime in your country. You may get into trouble for using these tools.
So, please do not use these tools for illegal works. As I already mentioned, you should never use the WEP encryption key in your home or wireless network. With available tools, it is child’s play to crack the WEP keys and access your wi-fi network.
Wireless monitoring and troubleshooting tools are basically for network admins and programmers working on wi-fi based software. These tools really help when some of your systems face problems in connecting to the network. I hope you enjoyed this article and got relevant information about popular wireless hacking and password cracking tools. I tried my best to compile this list of password hacking tools, but as a human error, I may miss something. If I forgot any important tool in this, please let me know in the comments. Pavitra Shandkhdhar is an engineering graduate and a security researcher. His area of interest is web penetration testing.
He likes to find vulnerabilities in websites and playing computer games in his free time. He is currently a researcher with InfoSec Institute. • Free Practice Exams • • • • • • • Free Training Tools • • • Editors Choice • • • • • • • • • • • • • Related Boot Camps • • • • • • • • • • • More Posts by Author • • • • • • • 6 responses to “13 Popular Wireless Hacking Tools [Updated for 2017]”.